Unsafe Legacy Renegotiation Disabled
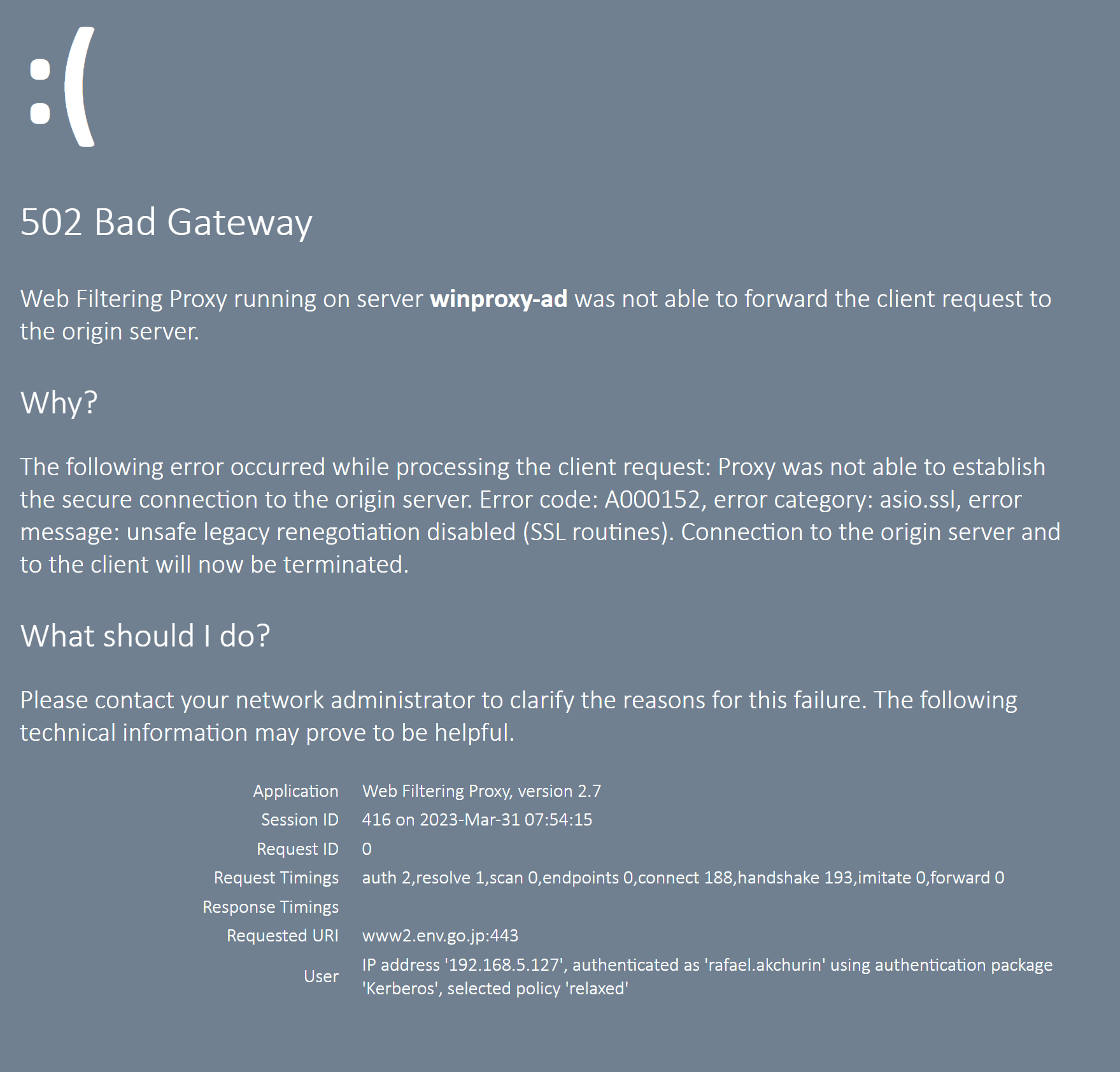
Sometimes browsing to a given site might result into the 502 Bad Gateway error with the following description text
Web Filtering Proxy was not able to forward the client request to the origin
server.
The following error occurred while processing the client request: Proxy was
not able to establish the secure connection to the origin server. Error
code: A000152, error category: asio.ssl, error message: unsafe legacy
renegotiation disabled (SSL routines). Connection to the origin server and
to the client will now be terminated.
The browser will then show a blocked page as on the following screenshot.
If you check the site in question using for example ssllabs.com TSL server test utility it will become obvious that the site has explicitly disabled the SSL renegotiation as explained in this article.
Latest version of OpenSSL 3 that is used in Web Filtering Proxy contains default setting that requires a remote site to unconditionally have support for secure renegotiation - which is recommended to improve overall security of the connections, described in OpenSSL 3 developer migration guide.
Secure renegotiation is now required by default for TLS connections
Support for RFC 5746 secure renegotiation is now required by default for
SSL or TLS connections to succeed. Applications that require the ability
to connect to legacy peers will need to explicitly set
SSL_OP_LEGACY_SERVER_CONNECT. Accordingly, SSL_OP_LEGACY_SERVER_CONNECT
is no longer set as part of SSL_OP_ALL.
Correct steps to mitigate this error is to tell the admin of the remote site to move to latest version of OpenSSL. If this is not possible, two other possibilities exist.
Option 1 - Add to Global Exclusions
Add the domain you need to connect to to Global Exclusions. This will force the proxy to treat this connection as opaque tunnel of bytes. Then your browser will decide if it is OK to connect to that domain or not.
Option 2 - Allow Legacy Connections
Enable support for SSL_OP_LEGACY_SERVER_CONNECT in Proxy Settings / Origin Connections as shown on the following screenshot.
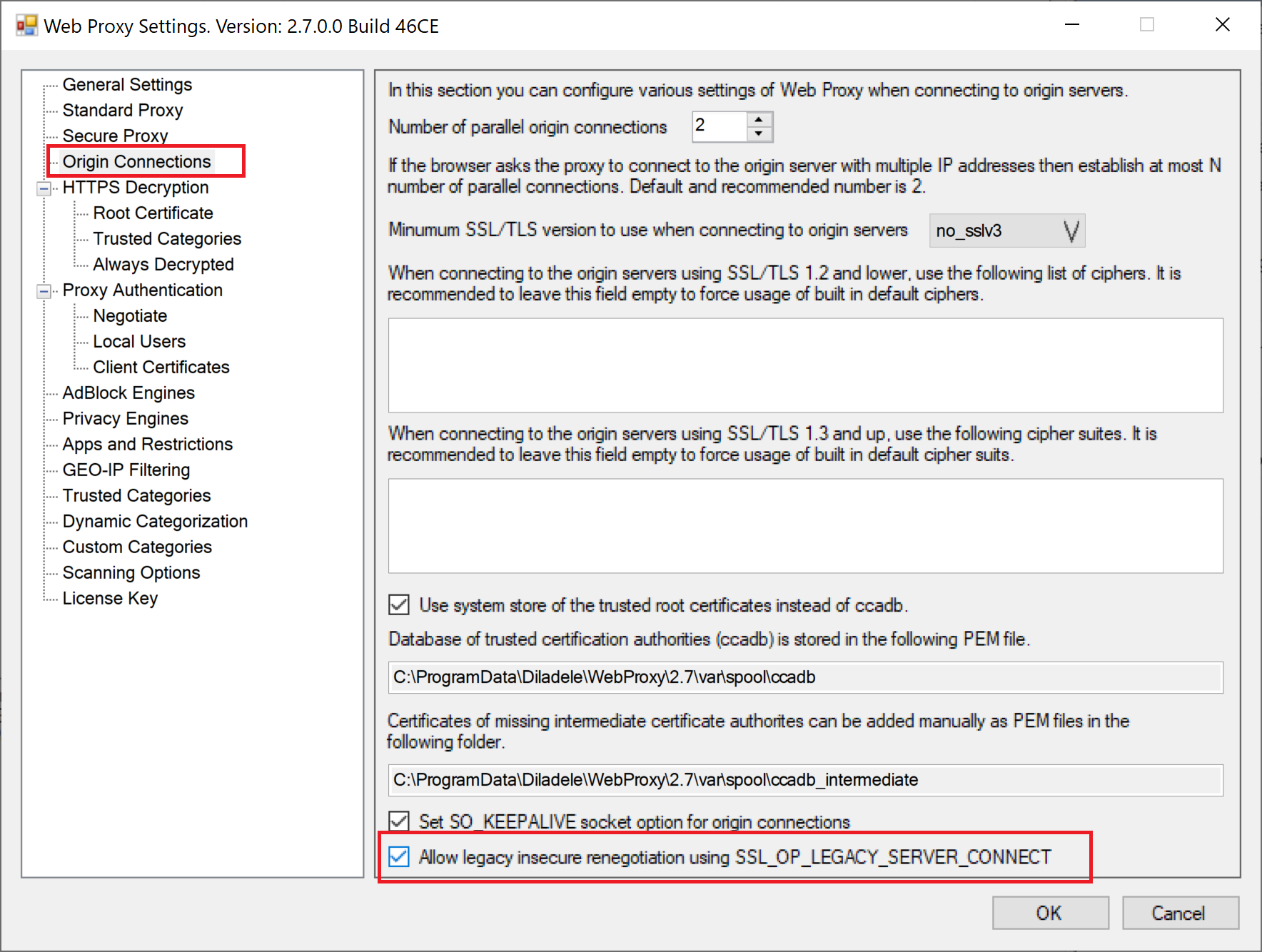
From now on the connection to the problematic domain will be allowed.